Article How to Launch a Successful Government BYOD Policy
State and local government IT departments are pressured on a number of fronts to meet greater demand as digital transformation continues to boom at all levels of government.
By Insight Editor / 4 Oct 2016 31 Aug 2017 / Topics: Modern workplace

These pressures include the need to incorporate the latest smartphones and tablets to create and access information, and accommodate the growing range of mobile devices employed by government workers, peer agencies and the constituents they serve.
The push for BYOD
With the growing prevalence of mobile devices in the government sector, such as the HP Elite x3, many state and local governments are acknowledging the value of a Bring Your Own Device (BYOD) policy.
From a generational perspective, baby boomers are entering their retirement years, opening state and local leadership roles for Generation X and millennials. Workers from these generations tend to embrace new technologies, often employing the latest devices for their personal and professional use.
4 guidelines for successful BYOD rollouts
Meeting demand for mobility, early adopters of BYOD programs have found solid ground by following these four guidelines:
- Establish a security mindset that acknowledges the challenges inherent to mobile devices while realistically and effectively mitigating as many risks as possible. For example, some state and local governments might choose to limit the initial range of devices to one manufacturer or operating system. This way, they can expand worker options in a controlled setting — supporting every platform and device would be an impossible task for any IT department.
- Clearly define you BYOD policy and obtain strategic buy-ins from officials who champion the changing culture. Well-defined and consistently communicated rules and expectations ensure workers and their managers engage BYOD programs with security and technology limitations in mind.
- Automate device security whenever possible by obtaining resources specific to mobile device and application management and security. This includes tools and systems that grant government IT leaders visibility into endpoint security to protect technology housing mission-critical information.
- Implement data loss protection methods. While the devices themselves have some value, they pale in comparison to the sensitive data they grant access to. Focus on tracking and setting up devices security measures to guard data as it moves from the network core to the edge and back. Ensure that almost no data is stored on the mobile device itself.
Each state and local government organization needs to define the limits of what they can securely support within their BYOD policy. IoT-connected devices that don’t have proper security features create additional intrusion vectors for cybercriminals. Finding trusted advisors to align technology trends and security capabilities to specific agency missions is critical to successfully planning and deploying a BYOD policy.
Managing device security for government IT solutions
While it’s widely recognized that the most important asset of any organization is its people, it’s also true that those same employees and staff are commonly attacked entry points. As mobile device adoption increases in the public sector, platform management and policies become every bit as important as firewalls and secure networks.
According to IBM, high-profile data breaches are increasingly common, costing an average of $4 million in damages, putting IT infrastructure under intense (often political) scrutiny. With the number of break-ins and the damage they cause on the rise, government IT departments are forced to perform a high-risk balancing act: driving more data, accessibility and capability while mitigating their agencies' or constituents' vulnerability.
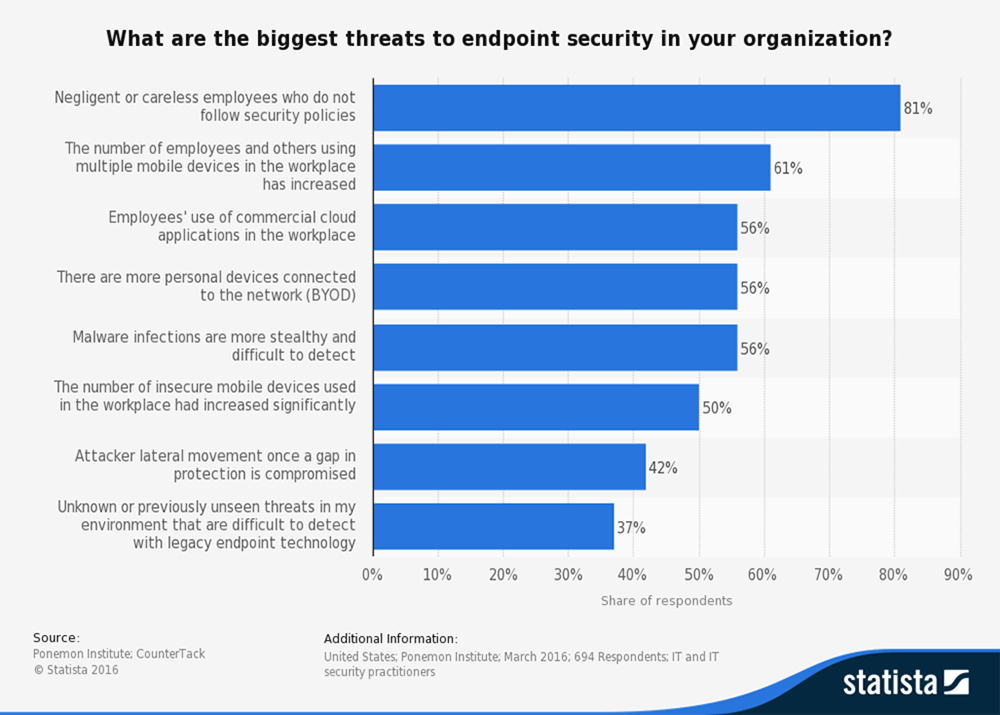
As shown in Figure 1, 56% of IT security specialists in the United States believed BYOD device practices were at the heart of endpoint security breaches in 2016.
Although efficient, a BYOD policy may expose state and local governments to security breaches. IT managers delivering new mobile devices must plan to mitigate increasing risks of data theft, fraud, insider threats and privacy breaches. Unfortunately, such security plans negatively impact agility and increase maintenance burdens and IT costs, adding another layer to the existing challenges of government IT services.
With mobile devices, security concerns expand beyond pure data management to device management. In order to succeed, government IT leaders must ask, "How do we secure mobile devices so that if someone leaves their device at a restaurant or friend's house or coffee shop, that device's information and network access is not compromised?"
As the number of foreign-owned device manufacturers increases, supply chain security also becomes a hot topic. Agencies are wise to vet technology vendors by asking, “How do you secure your supply chain?” Agencies need to ensure the security of network devices from the manufacture through installation and deployment. They must also combat instances where something embedded into the hardware or firmware of the device may present a security compromise. Therefore, device discovery needs to include a supply chain element that defines and tracks the logistical path of hardware, software and applications along their entire lifecycle.
Here again, an understanding of the missions served by state and local government IT teams requires a holistic and comprehensive security mentality that spans far beyond the firewalls of the network. Device risk management must peer back to the hardware vendors of such devices, as well as forward to their deployment for a mobile workforce and constituency.