Insight Managed XDR Security Services Service Engagement Framework
Executive summary
For Insight Managed Extended Detection and Response (XDR) Security Services, securing client environments and data are top priorities. As threats grow in number and complexity, we believe it has never been a better time to approach security as a pervasive component of every project, with every client. It is simply no longer appropriate to tack-on security as a single consideration or an afterthought.
In our pursuit to provide security leadership and proactive strategies, we share this framework to inform interested parties of our services and how they work. Primarily, we achieve our security objectives through applications and specific services like security monitoring, vulnerability scanning, and endpoint threat detection/protection.
We are firm believers that digital transformation encompasses people, process, and technology — the same can be said for security. Through our numerous solutions, we aim to empower people, improve process, and strengthen and evolve technologies in order to build a security program that withstands immediate and unforeseen threats.
Introduction
Insight Managed Extended Detection and Response (XDR) delivers cybersecurity monitoring with the combination of people, processes and technology. Here, we will review details of our managed security tools, services and processes. We then share information about our various security services as well as the service transition overview
Though our perspective here will be more narrowed than broad, we invite interested readers to explore our other materials that provide glimpses into the methods, strategies, and best practices we employ to support our clients in their information security journeys.
Managed Security Services
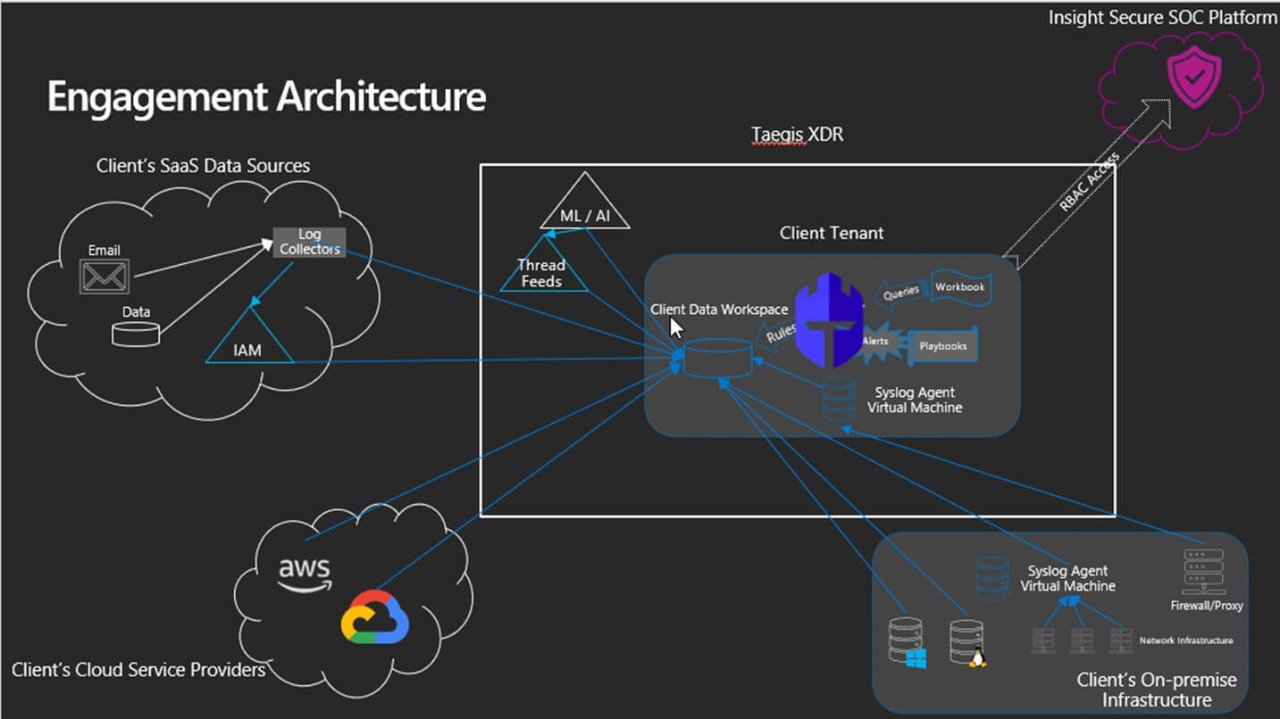
Insight Managed XDR utilizes industry-leading security monitoring applications to detect threats within the organization. The majority of the tools are SaaS-based, cloud-native with minimal on-premises footprint. Insight MSS uses a combination of SIEM, XDR, EDR, and Vulnerability Scanning applications to deliver its services.
Security is an ever-changing and always critical component of an IT organization. Insight consistently adapts existing security services, adds new capabilities, and stays current on ways to be proactive in this field. Below are a number of our specific security offerings that bring our clients peace of mind.
Security Operations
Our 24x7x365 Security Operations Center is comprised of tiered security analysts who are skilled and certified in various security disciplines.
Role based access control (RBAC)
MSS Support Services makes role-based access control (RBAC) which means users are assigned privileges based on job classification or function, not per specific employee demand, request, or preference.
SIEM / XDR
Through manual and automated daily log analysis, our security team detects suspicious activity in the environment and performs a response to threats. coordinates course-corrections. The technologies used to perform detections heavily relies on the data sources it collects logs from, and Insight provides consultative recommendations as to which data sources to include in monitoring for maximum effectiveness.
Security Training
All MSS Support Services engineers and contractors go through security awareness training upon hire and annually thereafter to provide a deepening, foundational platform of knowledge. Training is a series of modules — each module covers a specific human risk or compliance requirement and concludes with a quiz to measure learner comprehension. Furthermore, SOC personnel are assigned annual development programs to attain relevant certifications to better serve our clients.
MSS Tools, Services, and Processes
XDR
Service: Insight provides a co-managed, cloud-native XDR solution that partners with its clients to continuously enhance and update its detection capabilities. Our security solution offers around-the-clock detection. Through manual and automated daily log analysis, our security team proactively detects suspicious activity in the environment and provide recommendations for containment and remediation.
Insight MSS utilizes an industry-known platform named Taegis to deliver XDR services that provides intelligent security analytics for the entire enterprise, powered by artificial intelligence (AI). Taegis leverages AI to detect emergent threats and reduce alert fatigue. It can be configured to respond rapidly with built-in orchestration and automation. The platform allows security analysts to perform detailed security investigations and determine if a presented threat is legitimate or regarded as a benign or false positive.
Vulnerability Scanning
Vulnerability scanning should be at the base layer of any security program. Continuously remediating vulnerabilities is essential for protecting the IT environment. Regular vulnerability scans are performed — internally and externally — on the operating system, web application, and databases in the environment using a variety of tools. Insight has partnered with and utilizes Rapid7 for its vulnerability scanning offering.
Endpoint detection/protection
Most malicious activity occurs on endpoints. Legacy EPP products aren’t sufficient to detect threats. EDR solutions like Red Cloak and Microsoft Defender for Endpoints provide modern-day threat protection. Our security solution collects and automatically correlates data across multiple security layers – email, endpoint, server, cloud workload, and network. This allows for faster detection of threats and improved investigation and response times through security analysis.
Service Transition
Security is an ever-changing and always critical component of an IT organization. We consistently adapt existing security services, add new ones, and stay current on ways t be proactive in this field. The Service Transition phase consists of all one-time onboarding activities and is laid out by the following steps: Client Kickoff, Service Transition Plan, Service Transition Roles and Responsibilities, Service Transition Assumptions, Security Monitored Asset List, and Data Collection.
Client Kickoff
The client kickoff starts the Service Transition by arranging a meeting between the Client and Insight. The agenda consists of an introduction with the Insight service team wh will provide information on the servicing t include engaging Insight, planning and scheduling the Service Transition, and establishing remote access.
Service Transition Plan
Insight’s Transition Plan is broken down int the following steps: service initiation, data validation, Security Monitored Asset Configuration, process integration, systems integration, and normalization. The Service Initialization will start off the process, while other steps may occur in parallel. The approach is determined by the results of the Scope, Schedule, and/or Service Fees.
Service Transition Roles and Responsibilities
This area is detailed in the SOW and lists the roles and responsibilities of both Insight and the client.
Service Transition Assumptions
Below is a list of assumptions the client agrees t before the service transition begins:
- Service transition activity will only occur during business hours
- If operational assistance is requested by the client during Service Transition, Insight can deliver reactive services on a best-effort basis utilizing Service Hours
- Remote, network, and/or system access may need t be initiated by the client systems
- Service transition tasks are subject t client’s participation in the regularly scheduled Service Transition status meetings and completion of tasks assigned t client. Client’s failure t perform assigned tasks may delay the integration resulting in a longer Service Transition period
- Insight will activate the MSS when all phases of the Service Transition Plan are completed
Security Monitored Asset List
In this step the client is required t document all inventory/asset data on a provided Security Monitored Asset List. This list contains all of the client’s applicable networked devices detailing things such as their IP addresses, hostnames, operating systems, patch version, and levels of criticality for both on-prem and cloud infrastructure. If Insight needs t migrate and reformat data from a preexisting inventory list from the client, Insight will be required t consume Service Hours t complete the task.
Data Collection
The final step in this phase is t collect any data provided by the Client. This may include but is not limited to:
- Network Diagrams
- Previous security assessment results (e.g. pen test, posture assessment)
- Run books
The client will be responsible for maintaining all provided documentation and will notify Insight of any changes that need t be made.
Onboarding
Insight follows a standard set of processes for onboarding new clients that ensures a clear path through service transition. It is essential during this phase for Insight t detail a service transition timeline leading up t go-live targets for service delivery.
- Participate in SOW review process and addresses areas of concern
- Develop and participate in the new client onboarding process
- Ongoing improvement of the onboarding process
- Cross collaboration with other teams
- Partnership with deployment teams (e.g. Consulting & Professional Services)
- Ongoing improvement of the deployment best practices
- Develop and participate in the client offboarding process
- Ensure all steps are accounted for by SOC and relevant teams (e.g. Tech Services)
- Periodically (monthly) audit tools for missed decoms.