Blog Talent Shortages and the AI Shift: Rethinking Your SOC Operating Model
By John Giglio / 24 Feb 2026 / Topics: Artificial Intelligence (AI) , Managed services , Cybersecurity

Key takeaways
- A crisis of efficiency: The talent shortage isn’t just about headcount; it’s about the inability of human analysts to keep up with 10,000+ daily alerts.
- The Agentic SOC: AI agents reduce investigation times from 30 minutes to under 5 minutes by autonomously planning and executing investigations.
- Managed expertise: Building an in-house 24/7 SOC can cost up to $2.8 million annually, while Managed SecOps offers expert coverage for a fraction of the cost.
The cybersecurity talent shortage is a crisis of efficiency. Discover why the traditional SOC model is collapsing and how AI agents are reshaping defense.
The modern security organization is currently caught in a “perfect storm.” On one hand, threats are escalating in sophistication — often amplified by the same generative AI we try to use for defense. On the other hand, we have a global shortage of skilled talent, which leaves teams redlined and overstretched.
But let’s be real: the “talent shortage” narrative is a bit of a misnomer. It’s not so much a headcount deficit; rather, we have a crisis of capability and efficiency.
The cracks in the legacy SOC model

For years, we tried to solve the “more threats” problem by throwing more “eyes on glass” at screens. Spoiler alert: It failed.
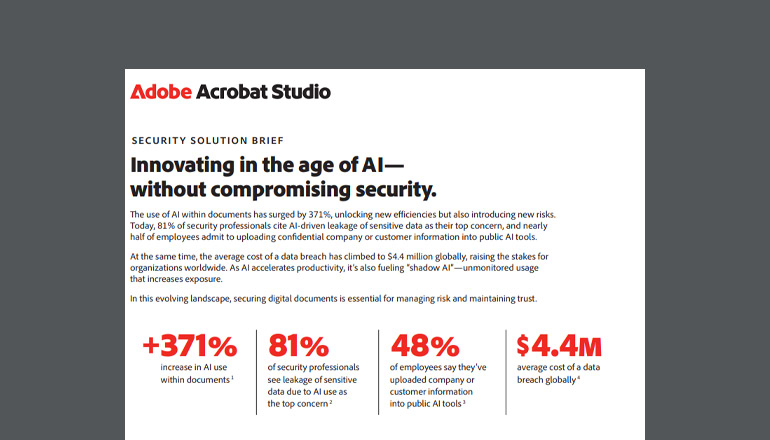
The traditional SOC model — built on a “pyramid” of Tier 1 analysts doing manual triage — is collapsing. The math just doesn’t work anymore. The average enterprise SOC receives thousands of alerts daily; for large organizations, that can exceed 10,000 alerts per day. No human army can keep up with that volume, which is why recent 2025/2026 data shows that 40% of alerts go uninvestigated, and up to 61% of teams admit to ignoring alerts that later proved critical because there’s simply no bandwidth.
The “external notification” gut check: If the “eyes on glass” model worked, we’d catch everything internally. But the data from Mandiant shows a different story: 54% to 63% of compromise notifications come from external sources — like law enforcement or the adversary themselves.
This is what we call a Schrödinger’s Job Market. The shortage is “felt” as burnout and unaddressed risk, but it’s not being acted upon with entry-level hiring because doubling a team that misses 60% of breaches doesn’t solve the core issue.
The force multiplier: Moving toward the Agentic SOC
We need a fundamental shift in how we operate. We’re talking about moving from rigid, playbook-driven automation (SOAR) to the Agentic SOC.
Unlike the old linear scripts, AI agents can autonomously plan, reason, and execute complex investigations. By leveraging Google Security Operations and Gemini, we’re seeing a total transformation:
- Autonomous triage: Specialized agents pull telemetry from identity, endpoint, and cloud sources instantly.
- Rapid investigation: We can reduce median investigation times from 30 minutes to under 5 minutes.
- Proactive threat hunting: AI agents can initiate hunts based on real-time intelligence from Mandiant and Google rather than waiting for a human prompt.
This effectively “decapitates” the traditional entry-level path by automating the grunt work that used to be the “apprenticeship” for new engineers. We’re moving from a pyramid workforce to a diamond shape: fewer juniors, but many more mid-level engineers who can manage these autonomous systems.
Overcoming the gap with managed expertise
Building a fully functional, 24/7 SOC from scratch is prohibitively expensive — we’re talking $1M to $4M annually. For most, the math just doesn’t work.
That’s why we’re seeing a massive pivot toward Managed Detection and Response (MDR). It’s about “buying” talent because “building” it has become too slow and risky.
| Cost Component | In-House SOC (Annual) | Managed SecOps (Annual) |
|---|---|---|
| Staffing (24/7) | $1.2M - $2.0M | Included |
| Technology Stack | $300k - $500k | Included |
| Total Estimated Cost | $1.65M - $2.8M | $120k - $560k |
By partnering with Insight for Managed SecOps, you aren’t just getting a vendor; you’re getting an operational extension of your team. We provide:
- Instant 24/7/365 coverage: Without the headache of staffing three internal shifts.
- Certified detection engineering: Our Google Cloud Solution Line team created 68 custom detections last year that identified incidents that otherwise would have gone completely undetected.
- Platform maximization: We ensure you get every ounce of value from your Google SecOps investment through continuous fine-tuning.
- Continuous threat hunting: Our team of threat hunters is constantly learning, watching, and applying their knowledge to all of our clients.
Overcoming the gap with managed expertise

The direct-entry cyber pro era is ending; the cyber-specialized engineer era is here. We must stop teaching manual log analysis as a primary skill and start teaching security engineering.
The bottom line: The SOC of 2026 isn’t a room full of people staring at screens. It’s a data center full of AI agents watched over by a lean, elite team.
Is your SOC operating model built for the AI era? Quantify the impact of modernizing your defense. Read IDC’s Business Value of Security Operations report to explore how Google Security Operations is transforming threat detection and team efficiency for global enterprises.
Are you ready to stop firefighting and start focusing on strategic risk? Reach out to us today to see how we can modernize your defense and quantify the impact of a Managed SecOps model.

 Monthly perspectives from global tech leaders.
Monthly perspectives from global tech leaders.