Article KRACK, WPA2 Security and You
With a growing number of cyberattacks, it’s no longer enough for businesses to merely hope their security programs keep them safe.
By Insight Editor / 3 Nov 2017
By Insight Editor / 3 Nov 2017

It’s not even enough to rethink their security programs. Today, businesses need to understand specific vulnerabilities to stay safe from cyber mayhem.
Let’s take a behind-the-scenes look at Key Reinstallation Attacks (KRACKs), as well as a recent cyber scare: an exposed weakness in WPA2 security protocols. Then, we’ll discuss tactical questions your organization can address to ensure your processes stack up.
On Oct. 16, 2017, security researcher Mathy Vanhoef found a flaw in the 802.11 protocol around rekeying, which could enable an attacker to perform a MITM attack to listen in on wireless traffic.
This type of attack occurs when a hacker intercepts communication between two users without their knowledge, rerouting each instance of communication to the attacker’s computer. According to Microsoft’s TechNet glossary, “Each user in the communication unknowingly sends traffic to and receives traffic from the attacker, all the while thinking they are communicating only with the intended user.”
By modifying Active Directory Domain Services, the hacker can add his or her server as a trusted network. Users unknowingly connect to the malicious server, exposing their data during the exchange.
To make matters worse, the 802.11 flaw is an issue with the actual protocol itself, making all devices relying on that wireless protocol susceptible to a MITM attack at some level. Several vendors, including Microsoft, Apple and Cisco, have already created patches to address this flaw and have published them to their user bases.
A resounding question from organizations is, “How concerned should I be”? The answer is every enterprise should take notice of this vulnerability due to the potential threat it brings — not just to the enterprise directly, but also to employees and their families whose data and surfing habits could be used for social engineering attacks down the road.
It’s important for IT organization to create a plan of action to address this threat within the company, providing education to their users on what to look for and how to protect themselves when they’re off the network.
Some questions to address include:
The Community Emergency Response Team (CERT) has published information about the vulnerability and a list of common vendors that could be affected. You can search for your company name to see if your devices are susceptible.
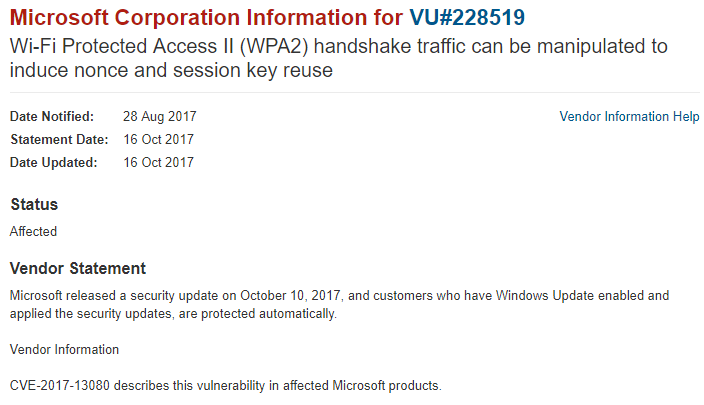
Figure 1 shows an example of a Microsoft search result. Additional details can be found on the link under Vendor References. The site provides information detailing the products affected and the mitigation Microsoft has already taken. On Oct. 10, Microsoft released a patch that addresses this vulnerability and followed up with subsequent security updates on Oct. 16 and 17.
For enterprises with the right tools in place, discovery of devices is a critical step to understanding your environment and where vulnerabilities may lie. Tools that can help you discover the systems on an enterprise network include:
With these solutions, your organization will need to determine the device operating systems (Windows, Mac OS X, iOS, Android, Berkeley Software Distribution (BSD), etc.) and their current patch levels.
This will help you put together a patch management plan based on the types of devices in your environment, such as workstations, wireless access points, wireless IP phones, smartphones and tablets. These tools can also help you identify unmanaged devices, where a manual effort will be required to determine device type and manufacturer, such as wireless security cameras, building management systems, medical devices, printers and more.
Because the best security program isn’t one-size-fits all, any security service provider must be knowledgeable in a wide array of security topics — including KRACKs, WPA2 security and MITM attacks — to help the enterprise craft a unique solution for the environment. Many out-of-the-box solutions run the risk of pigeon-holing the organization into a specific tool that may meet your needs in one area but not address the full gamut of possible security gaps.
Insight offers vendor-agnostic security workshops that evaluate your end-to-end processes and give detailed snapshots of overall system health. This not only helps your organization understand both the strengths and weaknesses of your environment, but also offers guidance to optimize processes without vendor lock-in.

Discover reports, stories and industry trends to help you innovate for the future.