Article How to Boost Your Healthcare Security Immune System
The healthcare industry is experiencing exponential progress in its digital transformation — but it’s not without growing pains.
By Jillian Viner / 31 Aug 2017
By Jillian Viner / 31 Aug 2017

Replacing old systems with information technology improves efficiency and patient care. However, an escalation of healthcare data breaches over the past year demonstrates the many security and compliance issues the healthcare industry needs to overcome.
Healthcare IT professionals face unique security challenges because sharing information is such a pivotal component of the industry. Additionally, organizations must comply with strict government regulations.
Practitioners need to be vigilant about protecting patient data. Building a multilayered, secure IT environment from the core to the application level is the only way to ensure patient information is readily available for the right people — and kept out of the wrong hands.
In 2016 alone, cyberattacks compromised more than 27 million patient records.
Verizon’s “2017 Data Breach Investigations Report” found that 15% of data breaches in 2016 involved healthcare organizations.1 The reason is twofold: The value of health records on the darknet makes them a lucrative target, and healthcare security is notoriously lagging in older equipment (both hardware and software).
Healthcare organizations are prime targets for malicious payloads and ransomware because of the valuable information stored in a healthcare record: not just insurance information, but also a patient’s Social Security number, driver’s license and credit card information — all of which can be sold on the darknet.
In 2016 alone, cyberattacks compromised more than 27 million patient records, according to a study by Protenus Inc. in collaboration with DataBreaches.net. A 2017 study by the Ponemon Institute found that healthcare organizations suffered an average cost of $380 per lost or stolen record.2
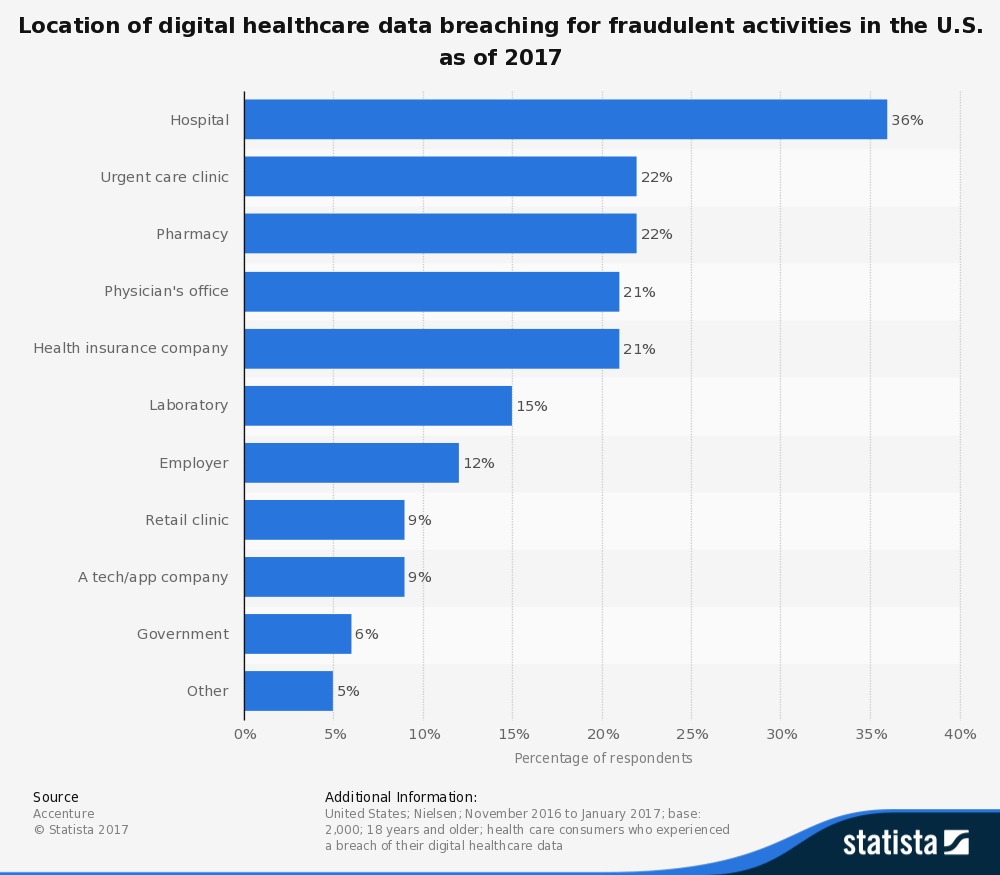
Even as healthcare security awareness grows, organizations have been slow to make necessary corrections. As Figure 1 shows, hospitals face the greatest security challenge ahead, absorbing 36% of healthcare-related data breaches, according to the 2017 “Digital Trust” report by Accenture Consulting. After hospitals, urgent care clinics (22%), pharmacies (22%), doctors’ offices (21%) and health insurance companies (21%) are the next targets.
The first step toward protecting patient information and reducing the risk of comprising data is a review of access control. The larger your staff, the greater the risk of a compromised login. The Verizon report found that 81% of hacking-related breaches occurred due to a stolen, weak or guessable password.
Not only are passwords a weak form of protection today, but they also create a poor user experience. For clinicians who may have multiple logins to access more than one Electronic Health Record (EHR), remembering and repeating logon and logoff processes invites human error. For example, a clinician might write down passwords and keep them near the computer or remain logged in to a system for convenience. However seemingly innocent, these are opportunities ripe for data breaches and noncompliance.
Recognizing the pitfalls of passwords, Single Sign-On (SSO) and multifactor authentication are emerging as new standards. Multifactor authentication solutions eliminate the possibility of compromised credentials either through cyberhacking (key logging) or human error.
For example, Intel and Microsoft have combined their technologies to create Windows Hello, a hacker-proof user identity and authentication solution that eliminates the need for passwords. Users can activate authentication via facial recognition, iris scans or fingerprint scanning. Once authenticated, Windows Hello is linked with Microsoft Passport, granting users immediate access to other applications and web services.
Touch-free authentication succeeds at both increasing security and providing a faster and more convenient solution for users, reducing the likelihood of risk-prone user workarounds. As an added bonus, the number of IT tickets for a password reset drops, saving IT teams time and money.
Vulnerable user credentials are just one potential attack surface for a security breach. To leverage other weak entry points for malware, cybercriminals continue to deploy phishing schemes — and users are still falling for them. In fact, according to the Verizon report, 7.3% — roughly one in 14 — of users will open a malicious link or attachment.
Educating, training and retraining staff about cybersecurity best practices is important but not a foolproof method of protection.
“Hackers will continue to go after networks, systems and applications that have been misconfigured or are not maintained properly,” reports MacMcMillan, co-founder and CEO of CynergisTek, in a HealthIT Security article. “Good cyber hygiene will become a common phrase to describe how organizations should approach managing the integrity of the enterprise.”
Having up-to-date hardware and software is vital for organizations to safeguard networks from cyberthreats. Better yet, having security software and hardware that work together creates the ultimate prescription to fend off threats.
New 7th Generation Intel Core vPro processor-based devices offer next-generation protection to boost Windows 10 security.
“The beauty of the Intel and Microsoft relationship is that we have our engineers and architects sit down and talk about the future and make sure the hardware and software work together,” says Chris Hubbard, Intel’s director of PC sales enabling for the Americas, Europe, the Middle East and Africa.
One of these collaborative security features is Windows Credential Guard. This security feature is an important sentinel against cyberthreats such as Pass the Hash (PtH). PtH attacks occur when a hacker gains access to one computer and steals an access token, opening the gates to a larger network. It’s easy to see why this is one of the most popular tools for attackers. PtH attacks are used in nearly all major breaches or advanced persistent threat-type attacks.
Windows Credential Guard uses virtualization-based security to isolate Windows authentication from the Windows operating system, thereby preventing PtH from occurring.
Cyber defense cannot rely on security software alone. Nor can it depend on hardware. Similarly, old hardware often doesn’t support security features offered by new software. To take full advantage of next-generation security, healthcare organizations must invest in security from the core to the application layer with up-to-date software and hardware working in tandem.
The initial investment in new technology can be a tough pill to swallow, but the benefits far outweigh the costs — especially when patient data is on the line. Refreshing your IT with new security software built in to Intel hardware and Windows 10 provides a formidable antidote to cyberthreats.
1 Verizon. (2017). 2017 Data Breach Investigations Report, 10th Edition. 2 Ponemon Institute. (June 2017). 2017 Cost of Data Breach Study.

Discover reports, stories and industry trends to help you innovate for the future.