Article Complete Security for Service Providers
When customers buy IT systems, telling them they need security solutions is like telling a home buyer they need locks on their doors.
By Insight Editor / 30 Sep 2016
By Insight Editor / 30 Sep 2016

The whitepaper, Discovering Your Security Services Sweet Spot, summarizes the many components of a comprehensive security strategy.
It explains how the security value chain begins with the user — even before they acquire a computer, tablet or smartphone. It also emphasizes documenting all corporate security policies and leveraging high-margin, high-value consultative engagements to help customers profit.
First, at the device level, you want to think about how users will authenticate themselves beyond an ID and password, how the network will make sure that the user is who they say they are and that the devices in use are compliant with the network’s required client configuration. Nearly 90% of enterprises say they have suffered at least one data loss through unsecure printers. It’s important to help customers calculate their risks and implement security measures for all devices on a given network.
Next, you want to outline how data must be protected at all times, whether in transit or at rest. Complete security solutions for the digital side include cyber security, network security, data security, cloud security and mobile security.
For the IT professional seeking the right security strategy to add comprehensive security to a portfolio of offerings, it’s also important to consider staffing, training and partnering with external experts for a more holistic approach.
When you only sell part of the security solution, you are actually failing your customers. While added benefits may raise the price of the system, they will reduce overall costs by detecting and preventing expensive breaches and dangerous data losses. Plus, the worldwide cybersecurity market has already increased from $3.5 billion in 2004 to $75 billion in 2015 with a forecast of reaching $170 billion by 2020. This indicates that companies today are more willing to spend money on reliable and secure solutions to combat rising threats.
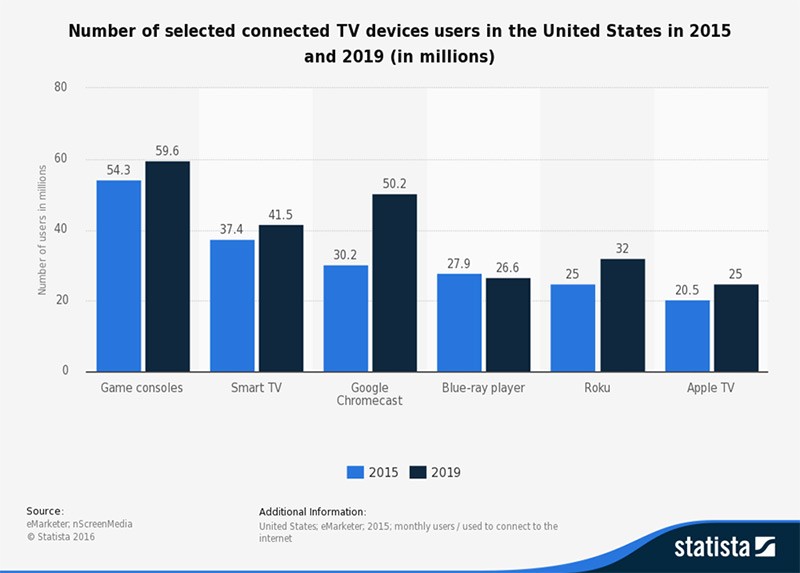
Cybercriminals have become more organized in their efforts to exploit users. It’s currently estimated that worldwide phishing sites will continue to pop up, amounting to over 290,000 domain names, costing businesses $2.1 trillion globally by 2019. As Figure 1 depicts, the number of connected TV users in the U.S. in 2015 and how the numbers are trending for 2019, the threat of security will only increase as more devices become ‘connected devices’.
Phishers send emails that look authentic, making claims that a user’s account has been attacked and the company needs the user to provide IDs and passwords or bank account numbers for re-verification. The user feels compelled to take “preventative” steps and complies, inadvertently giving the sender full access to everything the user was trying to protect in the first place.
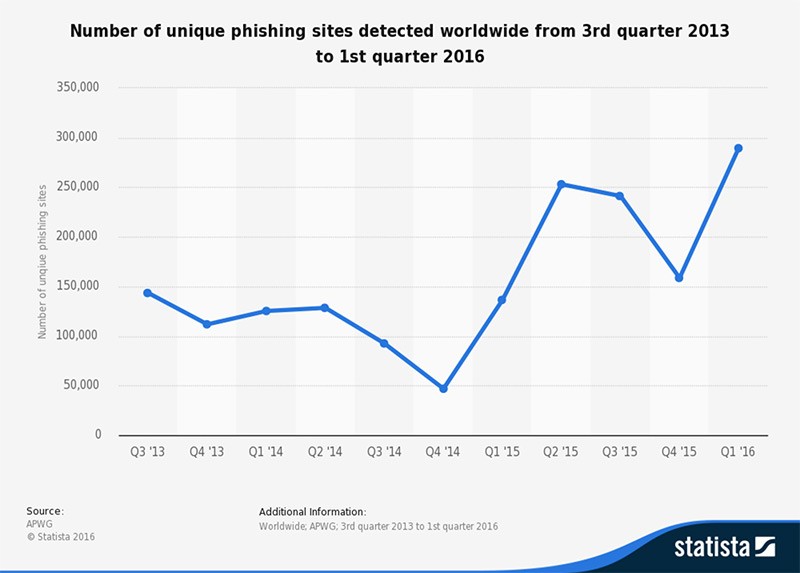
Phishing attacks happen every day and will continue to occur as more than 500 billion devices will be connected to the internet by 2030. As Figure 2 illustrates, the numbers were at their lowest in Q4 2014 at 50,000 sites and has hit it’s highest number in Q1 2016 at almost 300,000 sites and this is just just a fraction of the changes we can expect to see in the next three years. Imagine all of the sensitive information that will be lost and the number of businesses that will be victimized as more devices become end-points.
Businesses that install the best security systems and sophisticated encryption software, often assume that they have established complete security. However, truly secure solutions take into account both digital and physical security.
For example, imagine a doctor with extensive access to patient records. This particular doctor walks up to a data station in the hospital, logs in and retrieves the information he needs. Then, he walks away. A moment later, an orderly walks up to the same station, which is still logged on, and downloads a wealth of private patient healthcare information.
What about on the investment end? Picture a CEO of a large corporation going through the critical company data he needs to approve before the stock market opens the next day. He suddenly has to get up from his desk and take an urgent call outside. A passerby notices the opportunity, walks in and sits down at the CEO’s computer. In a matter of minutes, every piece of security investment and valuable information goes right out the window.
To prevent risks, every one of your corporate customers must have a complete security, data and network policy in place and have signed documents from all users confirming that they understand the physical and digital precautions.
Security policy development is a pure consultative service that is highly valuable to both customers and service providers. Everyone wins. Check out the whitepaper for more information on how you can successfully build a security strategy and secure client devices.

Discover reports, stories and industry trends to help you innovate for the future.