Future-ready solutions
With more than 20 years of experience and thousands of public sector and enterprise clients worldwide, Forcepoint has developed a versatile, powerful threat defense suite.
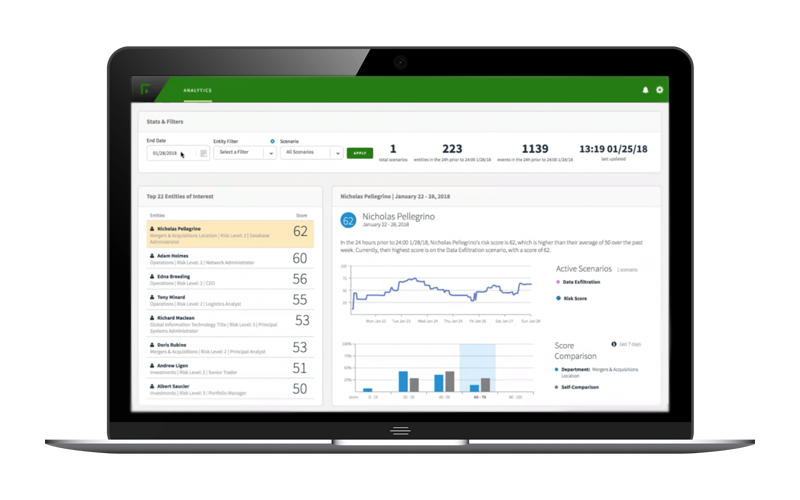
Robust detection
A systems-oriented method identifies compromised accounts and enforces policies rapidly.
Innovative tools
You can safely empower a workforce that’s modern, cloud based and application driven.
Actionable data
Advanced systems visibility enables better decision-making and more efficient protection.

Ironclad cybersecurity protection from Forcepoint
In the era of hybrid work and opportunistic bad actors, cyber defense has become more complicated than ever. The all-in-one cloud security platform Forcepoint® ONE makes it simple.

Boost productivity and mitigate risk.
Data protection shouldn’t get in the way of your business. By focusing on unified policies, user risk and automation, Forcepoint makes data security frictionless and intuitive
Always-on, resilient enterprise NGFW and secure SD-WAN
Sleep better at night with Forcepoint network security that blocks all invasion attempts and exploits, keeping you protected from cybersecurity threats before they emerge.